For years, the idea of an “attack surface” was closely tied to networks — open ports, exposed services, and internet-facing systems. In modern environments, that definition no longer holds. The most rapidly expanding attack surface today is not network-based at all. It is identity.
User accounts, service accounts, API tokens, OAuth permissions, temporary access grants — identities multiply quickly, but they are rarely managed with the same discipline. This uncontrolled growth is known as identity sprawl, and it has quietly become one of the most effective entry points for modern attackers.
How Identity Sprawl Becomes the Norm
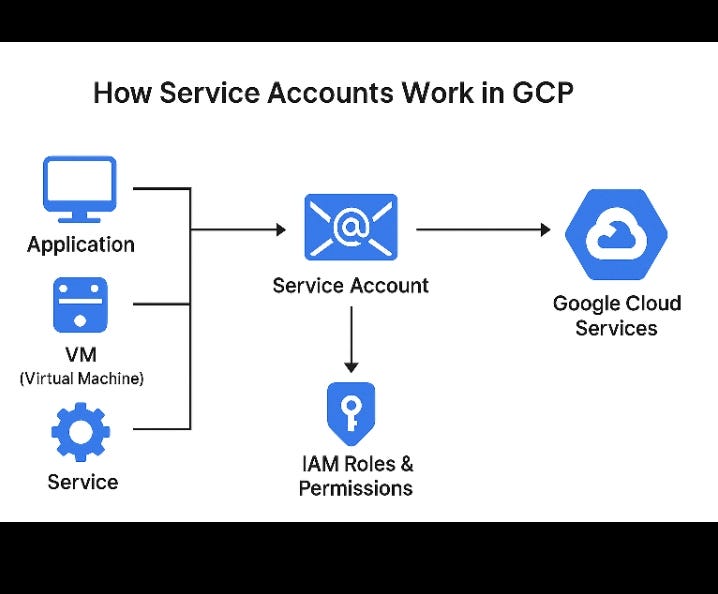
Cloud platforms, SaaS applications, and automation-driven workflows have made creating identities trivial. A new integration requires a token. A pipeline needs a service account. A third-party tool requests access. These identities are created to solve immediate problems, but rarely revisited afterward.
Over time, environments fill with accounts that no one actively monitors. Permissions remain in place long after their original purpose is gone. Ownership becomes unclear, and identity lifecycle management fades into the background. The result is not a single vulnerability, but a slow accumulation of unmanaged access.
Why Attackers Prefer Identity-Based Access
Modern attackers increasingly avoid exploits altogether. Instead, they rely on valid credentials and authorized access paths. From a defensive perspective, identity-based abuse is difficult to distinguish from legitimate activity. Authentication succeeds. Requests are authorized. Logs show nothing explicitly malicious.
Service accounts are particularly attractive targets. They often lack MFA, rarely rotate credentials, and operate continuously. API tokens with excessive permissions allow attackers to move laterally without triggering alarms. In these scenarios, the attacker does not break into the environment — they operate from within it.
Why Identity Sprawl Often Goes Unnoticed
One of the most dangerous aspects of identity sprawl is its invisibility. Security teams are trained to look for “bad” indicators: suspicious IPs, malicious domains, or known malware. Identity abuse rarely provides such signals.
Everything appears valid. Access is technically correct. Behavior fits expected patterns. The critical question is rarely asked: Should this identity still exist?
As long as that question remains unanswered, identity-based compromises can persist quietly and effectively.
Why the Problem Keeps Growing
Identity sprawl thrives on unclear ownership. Responsibility for identities is often split across IT, cloud teams, DevOps, and security. Everyone creates access, but no one truly owns it. Business pressure reinforces this behavior — if something works, it is left untouched.
Over time, this creates an environment where access outlives purpose. Identities remain active simply because removing them feels risky or inconvenient. Attackers benefit directly from this hesitation.
Conclusion
Identity sprawl is one of the least discussed yet most exploited weaknesses in modern security environments. It does not require advanced techniques or zero-day vulnerabilities. A forgotten identity with lingering permissions is often enough.
Modern attacks do not break down doors.
They use the keys — and many of those keys no longer have a clear owner.